Endpoint Central
De Complete Oplossing voor Endpoint Management
Endpoint Central biedt een alles-in-één oplossing voor het beheer van desktops, laptops, servers en mobiele apparaten. Van patchbeheer tot OS-imaging en mobiele device management – alles vanuit één overzichtelijke interface. Als officiële partner van ManageEngine in de Benelux biedt CBABenelux lokale ondersteuning, scherpe prijzen en uitgebreide onboarding.
Liever Endpoint Management in de cloud? Kies dan Endpoint Central Cloud
Probeer gratis
Waarom Endpoint Central
- Automatisch patchbeheer: Automatiseer het patchproces voor besturingssystemen en applicaties.
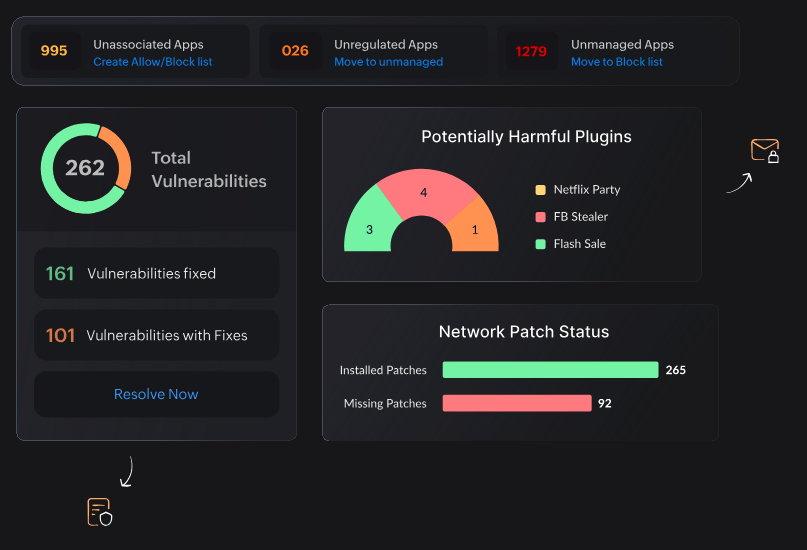
- Vulnerability Management: Identificeer en verhelp kwetsbaarheden op basis van risicoanalyse.
- OS Imaging & Deployment: Implementeer besturingssystemen en applicaties op afstand.
- Mobile Device Management (MDM): Beheer en beveilig mobiele apparaten.
- Remote Troubleshooting: Los problemen op afstand op zonder fysieke aanwezigheid.
- Endpoint Analytics: Krijg inzicht in apparaatprestaties en gebruikersgedrag.
- Geavanceerde beveiliging: Bescherm tegen ransomware, datalekken en ongeautoriseerde toegang.
Waarom CBA?

Lokale expertise: Onze consultants spreken Nederlands en begrijpen jouw IT-omgeving.

Scherpste prijs: Voordeliger – Geen concessies en meer service.
Volledige onboarding: Van installatie tot configuratie en training – wij begeleiden je stap voor stap.

Healthchecks & optimalisatie: Analyseer en verbeter je huidige configuratie met onze gratis healthcheck.
Vertrouwd door
Endpoint Central is een krachtige tool voor UEM die snel en gemakkelijk werkt
Met deze complete desktopmanagementsoftware beheer je naast Windows-, Mac- en Linux-besturingssystemen ook alle mobiele apparaten met iOS-, Android- of Windows, op een eenvoudige manier.
Je maakt bijvoorbeeld gebruik van profielen en beleid, configureert apparaten voor wifi, VPN en e-mailaccounts, stelt beperkingen in voor camera- en browsergebruik en beveiligt je apparatuur door het instellen van wachtwoorden, remote vergrendelen/wissen en meer.
Automatiseer je desktopmanagementroutine
Endpoint Central automatiseert alle reguliere beheerroutines voor endpoints, zodat beheerders zich kunnen richten op andere belangrijke taken.
Hierbij kun je denken aan:
- installeren van software, patches en service packs voor cliëntcomputers
- standaardisering van de desktops door het toepassen van uniforme configuraties
- beheer van USB-gebruik
- beheer van assets
- bewaken van softwarelicenties en software-gebruiksstatistieken
- controle van de netwerksystemen met complete hardware/software-inventarissen
- opsporen van verboden gebruik van software
- imaging en implementatie van besturingssystemen
- overnemen van remote desktops
Kortom, Endpoint Central helpt beheerders om te automatiseren, standaardiseren, beveiligen en controleren.

Ondersteunde Endpoints & OS
- Desktop / Laptop
- Telefoon / tablet
- Servers, IoT
- Rugged Devices en meer
- Windows & ChromeOS
- Linux
- macOS, iOS, iPadOS & tvOS
- Android

AI in Endpoint Central: Slimmere IT-Automatisering en Endpointbeheer
Met de groeiende complexiteit van IT-omgevingen hebben bedrijven behoefte aan intelligent beheer van endpoints. ManageEngine Endpoint Central integreert AI en machine learning om slimmere automatisering, snellere probleemdetectie en voorspellend onderhoud mogelijk te maken.
Hoe AI in Endpoint Central IT-beheer optimaliseert
✔ AI-gestuurde taakautomatisering – Voorspelt terugkerende IT-taken en stelt automatiseringsregels voor.
✔ Anomaliedetectie met machine learning – AI signaleert afwijkend endpoint-gedrag en waarschuwt IT-teams voor mogelijke dreigingen.
✔ Predictive analytics voor probleemoplossing – Voorspelt systeemfouten en adviseert proactieve maatregelen.
✔ Slimme aanbevelingen – AI leert van eerdere incidenten en stelt verbeteringen voor in beleid en configuraties.
Dankzij AI in Endpoint Central kunnen IT-teams sneller reageren op incidenten, beveiligingsrisico’s verminderen en meer doen met minder handmatige inspanning.
Compare editions
|
Endpoint Central
|
Endpoint Central Professional
|
Endpoint Central Enterprise(Distributed)
|
Endpoint Central UEM
|
|---|---|---|---|
| Automated Patch Management | |||
| Service Pack Deployment | |||
| Third-Party Patch Management | |||
| Server Application Patch Management | |||
| Antivirus Definition Updates | |||
| Test and Approve Patches | |||
| Install / Uninstall Software | |||
| Self Service Portal | |||
| 1300+ Pre-defined Templates | |||
| Modern Management for Windows 10 Devices | |||
| OS Deployment and Imaging | Add on | Add on | |
| HIPAA and PCI compliant Remote Control | |||
| Remote Control screen recording | |||
| Transfer Files in Remote Session | |||
| Voice and video call | |||
| Hardware and Software Tracking | |||
| Prohibited Software | |||
| Block Executable | |||
| Software Metering | |||
| License Management | |||
| USB Device Management | |||
| Power Management | |||
| Custom Scripts | |||
| Certificate Distribution | |||
| Printer Management | |||
| 100+ Predefined templates | |||
| Managing Desktops Across WAN | Limited | ||
| Manage Desktops of Roaming Users | |||
| Multi-Technician Support | |||
| Role Based Administration | |||
| Two Factor Authentication | |||
| Active Directory Authentication | |||
| Containerization | Add on | Add on | |
| Distribution Server for Bandwidth Optimization | |||
| Mobile Device Enrollment | Add on | Add on | |
| Profile Management | Add on | Add on | |
| Mobile Application Management | Add on | Add on | |
| Mobile Security Management | Add on | Add on | |
| E-mail Management | Add on | Add on | |
| Content Management | Add on | Add on |





